Information “at rest” refers to digital files (as well as hard-copies) which are being stored on devices or on paper or other formats.
In their digital format, information “at rest” refers to all our files (such as reports, evidence, fundraising or project proposals, contact information, accounting information, etc), their meta-data, our emails and attachments, text messages etc., stored on computers, phones, hard drives, USB-drives, SD-cards, CDs, “cloud” servers or those of our email providers, whenever they are not directly being transferred or communicated between devices. It is also worth noting that there can be lots of digital files at rest on portable devices, including smart-phones, whereby the data is at rest, but the device is in motion.
Hard copies of this data can be stored in filing cabinets, vaults, office desks, wallets, purses, shelves, books and ledgers.
Those opposed to the work of human rights defenders are often very interested in accessing such data: if captured, these sources can provide our adversaries with a wealth of information about our projects, movements or organisations. For this reason, theft and confiscation of computers, phones, and memory storage devices are common tactics used against human rights defenders. Others may try to break into our email or social networking accounts or cloud services, or try to pressure the companies through legal means into handing over our data.
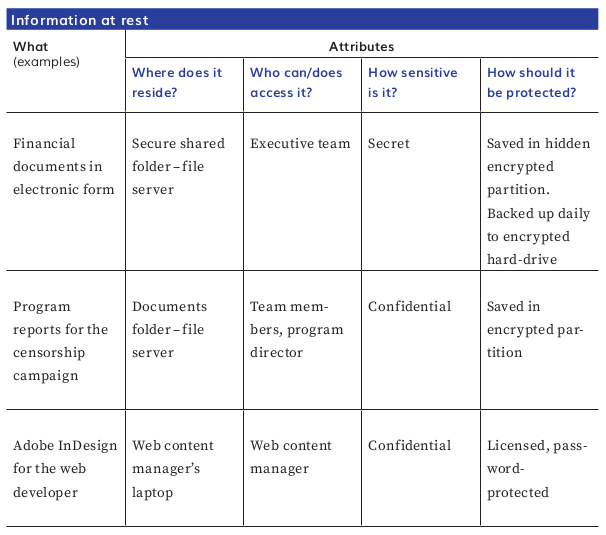
When brainstorming a list of your 'information at rest', it helps to consider some attributes, such as:
-
where they are
-
who has access to them
-
how sensitive is their content to you, your organisation or people mentioned in the document (e.g. witness or victim statements)
-
how important it is to keep them
-
how long they should be kept.
Try using a table similar to the one below to map your information at rest. Once you have taken account of at least your most important information and where it is, you can identify concrete ways of protecting it.
In the next section, we will consider how to map information in motion, how to map it, identify its vulnerabilities, and protect it.