Defining a comprehensive security strategy is significantly different to simply taking an ad-hoc or improvised approach to our security. Many of our instinctive reactions to threats or ad-hoc security protocols keep us safe but some of them don’t necessarily, and they may even be harmful.
We have already begun updating our security strategy by way of the new tactics and capacities we identified in the previous chapter. These should relate to an overall strategy to maintain and expand our socio-political 'space' for work as human rights defenders; this concept is expanded below.
Security strategies: maintaining space for our work1
Effective security strategies and plans must correspond to the specific political, economic, social, technological, legal and environmental context in which we operate. As discussed in Section II – Explore, political threats arise from other actors whose interests are potentially affected by our work, and who are therefore intent on closing the socio-political space we enjoy to carry it out. A security strategy helps us identify tactics to engage with our opponents in order to maintain or expand this space. It's useful to think of three broad categories of security strategies:
Acceptance strategies involve engaging with other actors (allies, neutral parties and opponents) to foster tolerance, acceptance and ultimately support of our human rights activities in society. This is often carried out through advocacy, campaigning, diplomacy and education activities.
Protection strategies emphasise learning or implementing new methods and practices which focus on defending our space for work. This can also mean leveraging the strength of our allies for protection and to bridge gaps in our existing security practices.
Deterrence strategies focus on raising the cost of carrying out attacks against us or our work for our adversaries, be that monetary cost, reputational cost or otherwise. These strategies also depend heavily on advocacy, campaigning, diplomacy and education activities, and require us to have a well-developed actor map in order to known which allies can help raise the cost of attacks against us.
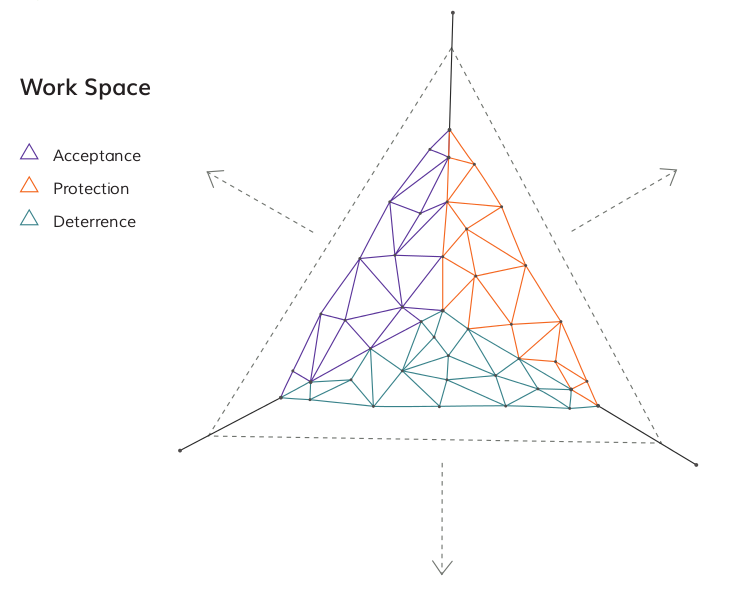
Many security strategies and plans will include activities which fall into two or all three of these categories: it depends, of course, on the context and threats identified. Try completing the following exercise to match the capacities you want to build (identified in the exercise Brainstorming New Capacities) with the strategic goals that best fit your work.
Capacity building & external resources
Once we have identified ways to address the gaps and vulnerabilities in our security in alignment with our overarching strategies, as above, we will likely need to engage in some form of capacity building. This might mean learning a new skill or it may require a long-term shift in how we go about our work. Consider the following factors which contribute to fostering behaviour change:
-
Well-being means having not only the conditions in our body and mind to go through a learning process actively but also having enough time and a safe space in which to learn.
-
Attitudes. To what extent do we consider this learning process to be valuable, useful and logical? Remember, attitudes are subjective and can be adversely affected by the experience of stress, fear and trauma
-
Knowledge and a strong understanding of our political, economic, social, technological, legal and environmental context give us a solid foundation upon which to build new capacities.
-
Skills are central to us being able to engage with and manipulate our environment. They might include physical fitness and self-care, political advocacy skills, technical skills like use of communication encryption, and so on.
-
Resources heavily influence the extent to which we can improve the elements above. Think about the resources available to you and your colleagues and how you can gain access to other resources for capacity buidling if necessary.
External trainings and consultants
Trainings and external consultants are often very useful in helping organisations and networks develop security plans and skills. This can be costly but it is worth budgeting for if you don't have anyone in-house who can provide the same skills or training.
The best consultants will empower you regarding your own security situation, rather than offering to implement a 'quick-fix' solution for you. Use them to get training on tools and tactics which you feel are relevant for your activities and bridge gaps in your existing security strategy.
External consultants should not conduct an analysis of your organisation's security practices without involving members of the group, nor should they make changes or take decisions for you. If they claim to be able increase your security immediately, you might need to keep looking! For in-depth guidance on what to expect from external consultants and what to avoid, download the full length Chapter here.
Choosing trainings or trainers
Friends, fellow human rights defenders, and trusted international organisations are good source of advice on choosing trainers or trainings on security. Try to have a clear idea about what you expect to learn but respect the opinion of the trainer in terms of what is achievable in a given time-frame. Consider what kind of experience or knowledge they should have before you decide to engage them. Consider elements like language, timing, location and options for follow-up; will you have time afterwards for practising or working with the new skills, knowledge or resources? Discuss these issues within the group to reach a solution which works well for everyone. If some members are disinterested it will have a negative impact on the training and will reduce the likely benefits that follow.
Material resources for security
Building and improving our security capacities can often have financial implications and may put a strain on already stretched funds. Whether it is the cost of new laptops to replace compromised hardware or the cost of a training, ultimately your safety may come at a price. For details of organisations which offer financial support to human rights defenders with security concerns, check out our Resources page.
1) For more in-depth information on acceptance, deterrence and protection strategies, see Eguren, E. (2009). Protection International, New Protection Manual for Human Rights Defenders, Ch. 1.6
